5 Common Mistakes to Avoid When Implementing Identity Verification Solutions
As digital transactions grow, organizations from all industries are moving to identity verification solutions to help thwart fraud, strengthen security, and cut down on customer onboarding times. However, adding identity verification solutions is not just selecting a provider and deploying their tech. Here are five common pitfalls to avoid when implementing an identity verification solution.
Overlooking ID Scanning Software Capabilities
ID scanning software is a vital player in identity verification at this time. However, most businesses miss out on the factors that make alternatives different. Some think that any scanning will reveal a fake ID, and others do not realize how discrepancies in capabilities and overall fraud detection have made some systems easily prey to fraud.
Organizations should procure effective scanning software with document authentication, facial recognition, and AI fraud detection features. Some ID scanning software solutions will assist in discerning security features on government-issued IDs before providing a complementary face match with documents and also track suspicious behavior through learning technology.
Choosing a Universal Approach
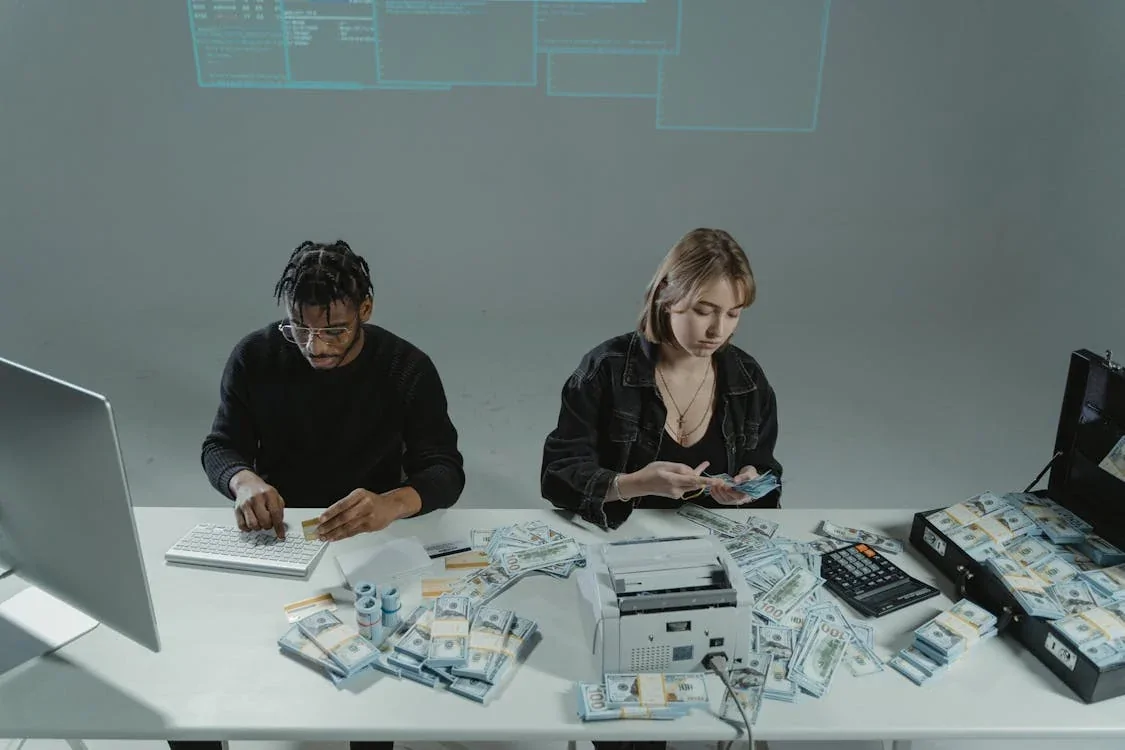
One of the biggest mistakes businesses make while implementing identity verification is taking generic solutions as the option that fits their needs. Every industry has different verification requirements. For instance, a financial institution is bound by Know Your Customers (KYC) and Anti-Money Laundering (AML) regulations, which call for full-cycle solutions of document verification, biometric checks, and real-time risk assessments.
Failure to choose an inflexible solution grants inefficient execution, escalates costs, and exposes the loopholes that compromise security. Organizations should thus assess their needs properly and choose a verification system that is in harmony with their industry-unique needs, requirements for compliance, and customer experience objectives.
Ignoring Compliance and Data-Protection Guidelines
Identity verification cannot merely be viewed as security; it also encompasses properly handling highly sensitive personal data in a legally compliant manner. Businesses that disregard regulatory requirements face heavy fines, civil suits, and a loss of reputation. Many regulatory laws exist to prescribe specific guidelines regarding the collection, storage, and processing of user data.
The consequence of failing to comply can lead to security breaches along with loss of trust from customers. Companies should ensure that their ID verification processes adhere to the law and that data protection is considered first.
Creating Friction for Users
Security is vital, but it will lose customers if the latter tends to make identity verification rather cumbersome. Many companies tend to place severe checks, resulting in high abandonment rates. Lengthy manual document examination, excessive document requests, and non-intuitive interfaces frustrate users, dissuading the completion of transactions.
To find the right balance between security and user experience, businesses should consider utilizing solutions with instant verification powered by AI, mobile-friendly interfaces, and biometric authentication. AI will review the documents and verify identities in real-time, resulting in a shorter wait and more commercial efficacy.
Not Updating and Improving Verification Methods
With the development of cybercriminal tactics, identity fraud mechanisms also become much more sophisticated. The other big blunder commonly made by businesses is to take the implementation of an identity verification system for granted, even though once an identity verification system is introduced, it will never work well again. They tend to leave specific emerging threats undetected by their outdated nature, like deepfake technology, synthetic identities, and more advanced document forgery.
To stay ahead of fraudsters, businesses must regularly refresh identity verification software and incorporate some means of AI-driven threat monitoring. Real-time analysis of new fraud patterns and dynamic adjustments of its detection capabilities are typical for several modern verification systems using machine learning.
Endnote
Identity verification solutions are necessary for this digital economy, while poor execution could lead to grave troubles. By preventing these mistakes, businesses can protect themselves from fraud while providing a seamless experience to their legitimate users. An effective identity verification exercise guarantees enhanced security and builds customer trust and credibility, thus creating a ground for long-lasting success.



